In 2026, cybersecurity threats are constantly changing as technology advances.
Cybercriminals are getting smarter, so it’s crucial for people and organizations to keep up with potential risks. Knowing the latest trends and threats helps protect digital assets.
We can expect new vulnerabilities and attack methods, but being ready can make a big difference.
Overview of Cybersecurity in 2026
In 2026, the cybersecurity world is changing quickly.
With new technologies like AI, 5G, and IoT, there are more opportunities for cyber threats.
While these technologies are helpful, they also bring new security challenges for both professionals and regular users.
Cybercriminals are using more advanced techniques to break into systems, so it’s important to stay updated on these threats and take steps to protect sensitive information.
Major Cybersecurity Threats in 2026
In 2026, several emerging threats will dominate the cybersecurity landscape, each posing unique risks to individuals and organizations. Understanding these threats is the first step in developing effective protection strategies.
1. Phishing
Phishing remains one of the most pervasive cyber threats. In 2026, phishing attacks have become more targeted and convincing, often mimicking legitimate communications from trusted sources.
Attackers frequently use social engineering tactics to trick users into revealing sensitive information, such as passwords or financial details. Sophisticated phishing attacks can even bypass traditional security measures like spam filters.
2. Ransomware
Ransomware attacks have not only increased in frequency but also in complexity. Cybercriminals now target critical infrastructure and large organizations, demanding hefty ransoms in exchange for decryption keys.
The sophistication of ransomware variants makes it difficult to recover data without paying the ransom, which can have widespread financial and operational impacts.
3. AI-Driven Attacks
The use of AI by cybercriminals is on the rise. AI-driven attacks can rapidly analyze and exploit weaknesses in networks and systems. These attacks can be automated, making them faster and more efficient.
AI technology is also used to create more convincing deepfake videos and audio, further complicating the fight against disinformation and fraud.
4. Deepfakes
Deepfakes have become a significant concern as they become more realistic and easier to produce. Cybercriminals can use deepfakes to manipulate audio and visual content, compromising a person’s or company’s reputation.
They can also be used in scams, such as business email compromise attacks, where fake videos or audio clips are used to deceive employees into making unauthorized transactions.
5. IoT Vulnerabilities
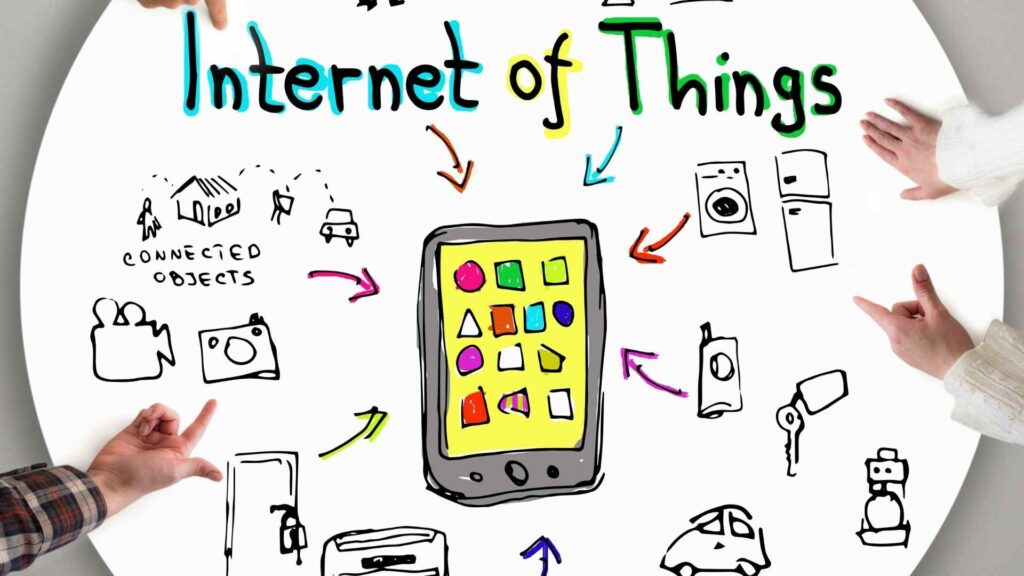
With more IoT devices around, cyberattacks have more opportunities. Many IoT devices don’t have strong security, making them easy targets for hackers. Hackers use weaknesses in these devices to break into networks or start bigger attacks. As more devices connect, it’s crucial to secure this IoT network to avoid security breaches.
Keeping up with new threats means using better security practices, constantly watching for problems, and teaching users how to spot and deal with attacks effectively.
How to Recognize and Avoid Common Cyber Attacks
In today’s digital world, it’s crucial to recognize and avoid common cyber attacks. Knowing the strategies used by cybercriminals is the first step in protecting yourself online.
Phishing is a common cyber threat involving fake messages that look like they’re from trusted sources. These messages often ask you to click a link or download something, which can lead to malware or stolen data. Always check emails and messages for any requests for personal information or strange links. Watch out for bad grammar, URLs that don’t match the source, and odd sender addresses—these are signs of phishing.
Moreover, Social engineering attacks trick people into giving confidential information. Be careful of unexpected calls, emails, or visits from people who say they’re from real companies. Always confirm who they are before sharing info.
Additionally, passwords are often targeted using brute force or credential stuffing. Use complex, unique passwords for each account and turn on two-factor authentication to help protect yourself.
Furthermore, Supply chain attacks are a growing issue, where attackers get into networks through third-party service providers. To prevent these, make sure the companies you work with have strong security practices, and regularly check your digital supply chain for weaknesses.
By understanding and watching out for these threats, you can better protect yourself and your organization from cyber attacks.
Essential Tools and Practices for Personal Cybersecurity
Securing your personal digital life doesn’t have to be daunting. By employing essential tools and adopting safe practices, you can significantly bolster your cybersecurity defenses.
- Antivirus Software: Installing antivirus software is fundamental to protecting your devices from malware and viruses. Regularly update your antivirus program to ensure it can counteract the latest threats.
- Firewalls: Utilize firewalls to create a shield between your computer network and potential threats. They monitor incoming and outgoing traffic and block suspicious activity.
- Password Managers: Employ password managers to generate and store complex passwords securely. These tools can help eliminate the need to remember multiple passwords and encourage the use of robust credentials.
- Virtual Private Networks (VPNs): A VPN encrypts your internet connection, safeguarding your data from prying eyes, especially on public Wi-Fi networks.
- Regular Updates: Always update your software, operating systems, and applications. Developers release patches to close security loopholes that attackers may exploit.
- Data Backups: Regularly back up important data to counteract the effects of ransomware attacks. Having secure copies of your files means you won’t lose everything if an attack takes place.
In addition to using these tools, adopting good cybersecurity habits is crucial. Be wary of unsolicited emails, maintain a healthy level of skepticism about unusual requests for information, and educate yourself on the evolving landscape of cyber threats.
Together, these tools and practices can help you cultivate a robust personal cybersecurity strategy, keeping you safe in the digital age.
Steps Others Are Taking to Protect Against Cybersecurity Threats
In today’s digital world, both organizations and individuals are actively working to protect against cybersecurity threats. To stay ahead, it takes dedication, innovation, and sophistication. Here are some common strategies being used to boost cybersecurity:
- Continuous Monitoring and Risk Assessment: Companies are using systems that constantly monitor for unusual activities to quickly detect breaches. Regular risk assessments help spot vulnerabilities and strengthen defenses.
- Multi-Factor Authentication (MFA): Moving beyond just passwords, MFA requires users to confirm their identity in more than one way, like using biometrics or a temporary code, adding extra security.
- Employee Training and Awareness: Educating employees is vital since they can be a weak link. Regular training and simulated phishing attacks help employees recognize and counter threats.
- Advanced Encryption Techniques: More advanced encryption is used to protect sensitive data. Even if data is intercepted, encryption keeps it secure.
- Collaboration and Information Sharing: Companies work with partners and share information about threats to stay updated and adjust their strategies.
- Incident Response Planning: Detailed plans are created to manage and reduce damage if a breach happens.
These steps help protect data and build systems that can handle advanced cyberattacks. Individuals should also take similar steps to keep their personal data safe online.
Conclusion
Cybersecurity is always changing, with new threats appearing alongside old ones. To stay safe, everyone should keep up with these risks.
Updating software, practicing good cyber habits, and being cautious of phishing scams and social engineering are key steps in protecting yourself.
By taking these proactive steps and staying informed, you can use the internet more securely and confidently.










